Viro staff wishes you a happy Easter!


Viro staff wishes you a happy Easter!

Are you looking for a way to make your agile transport vehicle more secure without having to remove and replace a padlock after each opening?
Discover the 3 strongpoints of the new Van Lock Compact fastening unit, which is ideal for small-medium vehicles and the “brother” of the well-known Van Lock (which is more suitable for medium-large vans and, with the relative accessory item 4222.2035, also for trucks).

Viro Club wishes you a merry Christmas and a happy New Year.

Those who regularly go to the shooting range or those who wait for the resumption of the hunting season every year need to minimize the risks, always handling their weapons with maximum safety.
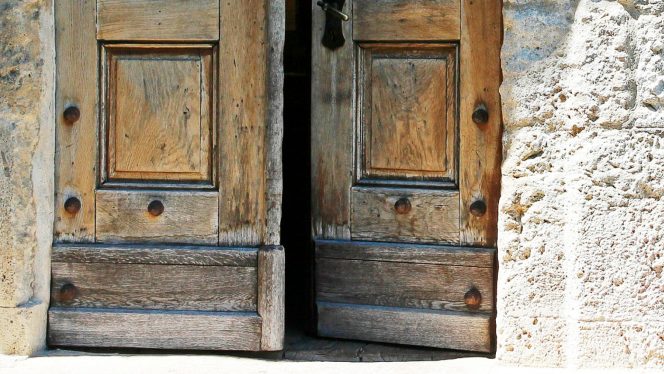
In the last article we spoke about mechanical safety locks suitable for installation on secondary wooden doors, such as cellar doors, garages and sheds. Now let’s see the most suitable electric locks for condominium wooden doors.

This short article provides an answer to the many users who ask us which security solutions are best suited for wooden doors. In particular, we look at the Viro locks for internal and external wooden doors and gates, of the swing or sliding types.
Rim or mortise locks suitable for:

In this article we will find out the differences between the TSA approved locks and the other common locks, plus, we will show you how to change the combination of a Viro TSA approved lock.
The beginning of the autumn season, like every year, marks (for many) the return to routine, resulting in a slowdown in tourist travel and a consequent greater offer of advantageous proposals to travel to the USA or to more remote destinations, perhaps making a stopover in one of the many American airports.
To travel to the United States it is absolutely recommended to close your suitcases with TSA locks for the reasons that we will see below.
Continue reading
The aim of the “Security Tips” series is to reveal some of the “trade secrets” to be able to identify a good quality security product quickly and without having to disassemble it.
We answer the most common questions about padlocks, locks, safes and other security devices, aiming to offer the possibility of an informed choice.
In this second episode we talk about the locks to be fitted and the reliability of the locking mechanism.

Three other useful warnings:
1. Always pay attention to the gestures we generally perform automatically. A substantial percentage of unwantedintrusions into the home occur through adoor or a window unintentionally left open. What may seem like carelessness, a minor oversight, such as forgetting
2. Taking care of the garden, decorating the entrance, perhaps with an automatic light, and emptying the letter box periodically, gives the idea of an inhabited house. An increased likelihood of running into someone during an attempted burglary does not encourage a potential thief to operate.
3. Managing the privacy of one’s social media accounts. Through social media we can make our location public, as well as every minor movement but, in terms of security and theft prevention, this would not be the best behaviour to have. In our opinion it is not necessary to deprive oneself of sharing a holiday photo on the Internet, but it is useful that only a limited number of people can view it. Almost all social networks allow us to choose the privacy setting we prefer.