In this fourth and penultimate article of the series dedicated to the characteristics which distinguish high security European profile cylinders we will conclude the analysis of the measures which obstruct opening with dexterity, focusing on systems which can deal with an increasingly widespread and insidious technique: key bumping.
The features which obstruct opening by using dexterity – Part II
After seeing in the last article how a cylinder can be protected against attempts to open with a tensor and lock pick, this article looks at key bumping, which is a particularly dangerous method as it can be very quick and usually requires less skill compared with lock picking.
Anti-bumping systems
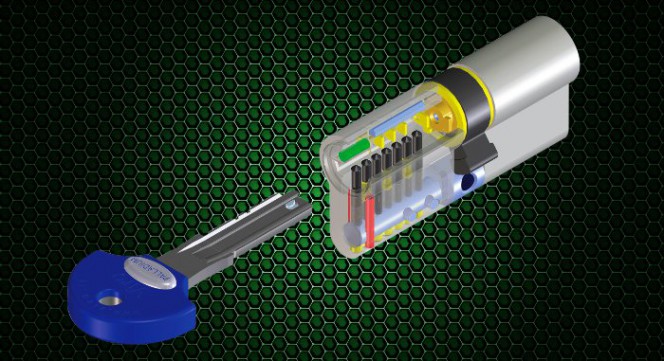
Key bumping uses the blows made with a specially encrypted key to retract all the counterpins into the body and to release for a fraction of a second the rotation of the plug. In order to counteract this technique, the high security cylinders adopt technical solutions which make it particularly difficult, if not practically impossible, to simultaneously align all the counterpins in the open position.

The key bumping method consists in using a key that is specially prepared for each specific model of cylinder which, when struck with a hammer, allows the counterpins to be pulled out and the rotation of the plug to be released for a fraction of a second.
Amongst the various ways to make cylinders resistant to key bumping it is possible to insert pins or other types of mechanical devices manufactured in a different way and/or placed on different axes compared to the traditional pins arranged on a single axis, so that the blow imparted by the bump key cannot move them all at once. A special combination of these solutions is, for example, used in the Viro Palladium high security cylinders.
Another system may be to match the pins with rotating pins activated by a desmodromic key, like those used on modern cars.
Or, alternatively, magnetic elements may be inserted which cannot be aligned by a bump key, but require a key with the correct magnetic encoding.
Conclusions
A high security European cylinder not only withstands well any attempts to open by brute force but is able to deal effectively with the various techniques of opening with dexterity, such as lock picking and key bumping.
But all this is useless if it is possible to obtain illegal copies of the key, because if a thief manages to come into possession of a key then obviously no protection is sufficient. We’ll see how it is possible to avoid illegal copying of keys in the next and last article of this series.
>> Read also: “How do you recognise a high security European profile cylinder? – Part V”
See the characteristics of the Viro Palladium high security cylinder
Watch the video presentation of the Viro Palladium high security cylinder